 Tough Times, Great PR book out!
Tough Times, Great PR book out!
Tough times call for tough measures, and these lessons can be good foundations to supplement businesses large and emerging.
Public relations (PR) builds brands, nurtures sales and opportunities, and protects the reputation of businesses. PR is a sustained effort nurtured by the C-suite, international communications and external specialist partners.
Following the good reception of the two earlier Dot Zen books, this book continues a journey through the years of a global pandemic, trade wars and conflicts, with a three decades old PR and strategy consulting firm staying afloat and helping clients grow together through the crises with good publicity, brand building, and reputation management.
What were the lessons learned during these crises? How can we benefit from them to nurture and build brands for the long haul? This book serves as an anthology of easy-to-read pieces to stir the imagination with ideas for the C-suite executives and business leaders, peppered with calligraphy and little “Dot Zen Moment” thoughts throughout the book.
Find out more!
More than a trainer or a speaker
You get insight, vision, foresight, leadership, historical perspective, anecdotes, stories, and humor – all from a single session, whether “live” or on “Zoom”. Unlike some, I have first-hand experience in many business and practice areas to give you REAL, actionable, and meaningful counsel. Short, punchy, inspirational. And now, in a “travel-lite” world, I am happy to speak to your audiences through “Zoom” or livestreaming.
More than a publicist or CMO
You get creative direction, field-proven business strategy, cutting-edge ideas to propel your marketing and communication to a whole new level. Excite and engage your customers and prospects, with the best Red Team you can get.
More than a web or cybersecurity consultant
You get C-suite strategy, content recommendations, tech and cybersecurity expertise. Professional web, e-commerce, cybersecurity, and digital marketing for the 21st century.
Hi! I am Seamus, your Communications and Red Team guy.
I was born severely premature in Taipei, when the attending surgeon told my family I could die. I didn’t, but faced many physical challenges throughout my earlier life. Through a disciplined life of diet, nutrition, contemplation and exercise, I subdued my physical challenges. I competed in 100-meter sprinting, pounded weights in the gym, learned Goju-Ryu Karate (one of the foremost Okinawan Karate paths, 剛柔流空手道), and later Muay Thai.
When I was in junior college, I spent way too much time on biochemistry research (on food lipids and autoxidation). I served in the army and came out confronted by the worst economic crisis in the 1980s.
However, I don’t believe life is meant to be wasted. Everyone has challenges. Every event in life has a Divine reason. And you can fight your way through. That’s what I bring to the table, the professional who will keep going.
Today, I spend my time as a thinker and practitioner in leadership, Internet, marketing, branding, and philosophy. For like minds among clients and eager learners, I’ve shared my life experiences, through inspiring and practical ways and speeches. Many clients also rely on my natural abilities to identify weaknesses and vulnerabilities in their business approaches and strategies. I am your RED TEAM consultant, your fractional Chief Marketing Officer (CMO), your business strategist, your Human Resource Development (HRD) specialist, business and digital transformation strategist, and more.
Leadership Keynote Speaker and Leadership Consultant
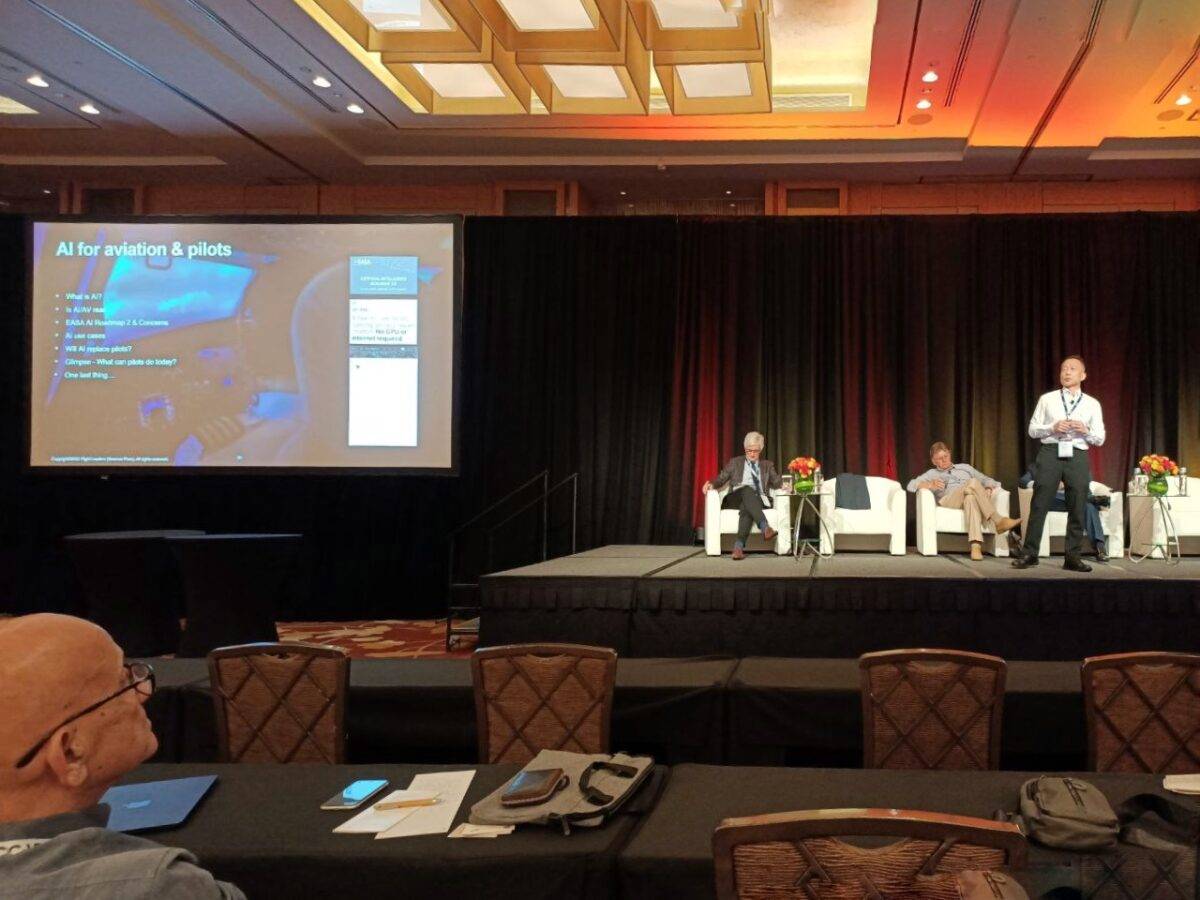
I specialize in delivering inspiring, enriching, and thought-provoking speeches for business leaders. I tell stories. I share anecdotes. I meld 4 areas from my unique background together – leadership experience, pioneering new economy knowledge, communication skills, and research. I speak in Singapore, and the region, especially Japan, Taiwan, Malaysia, Thailand, and continental Europe if need be. In a video-centric world, I am happy to deliver a keynote through “Zoom” or other livestreaming platforms.
Have me as a consultant, speaker, or your Fractional Chief Marketing Officer (CMO):
- AI and leadership transformation (artificial intelligence, machine learning, and trends for various industries)
- Leadership and Business Transformation (based on aviation and ancient Asian philosophies of Analects, Hagakure and Gorinosho)
- Sales Leadership (tactical sales training for knowledge workers and motivated salespeople)
- Media Training and Crisis Communication (with decades of first-hand experience from TV, radio and print journalism and media communication)
- Digital Marketing (with decades of being a digital PR and digital marketing pioneer in all areas of web development, SEO, content amplification and site optimization)
- Cybersecurity (having been a cybersecurity developer and sysadmin since 1996, and kept up with all emerging trends and current technologies)
If you want to expand and accelerate your business and brand, and would desire a fractional Chief Marketing Officer (CMO), I will be your best investment for Asia Pacific and beyond.
Award-winning
I have been inducted in the 500 Profiles in Excellence, humbly amongst the likes of Nobel Peace laureate President Kim Dae-Jung (Korea), artist Peter Gabriel, “Seven Years in Tibet” movie director Jean-Jacques Annaud, Cardinal Jan Peer Schotte (Sec-Gen of the World Synod of Bishops), and futurist Sir Arthur C Clarke. I was also a Barons 500 Leaders of the New Century inductee, humbly alongside the likes of leading futurist and visionary Sir Arthur C Clarke and Bill Gates of Microsoft. I have had been a Professional Member in the prestigious National Speakers Association USA for 20 years (since 2003).
Knowledge is my passion in life, and consequently I built knowledge-based businesses. I was the first Asian to be honored as a top business owner and coach by Business Owners’ Idea Cafe, a web resource highly rated by Wall Street Journal, Fast Company, Inc Magazine, Dow Jones, SF Chronicle and USA Today. I was featured as a Brainstormer in Seth Godin’s eBook “BullMarket 2004” (featured on Fast Company). I have done extensive radio reporting and TV commentary work with stations such as TechTV, CNA938 FM, Capital 95.8 FM, CNA, and CNBC.
Acclaimed Book Author
 I have always loved writing, and have been a published author since 1995, and a blogger since the late 1990s. I co-authored the book “Dot ZEN,” a leadership and entrepreneurship book aimed at small business owners, high-tech startups, knowledge entrepreneurs, and senior executives, to help them see a whole new way of managing marketing, publicity, public relations (PR), branding, human resources, entrepreneurship, and the use of the Internet, in a non-aggressive, enlightened manner. The book was based on 30 years of collective experience between us, when serving corporations and clients. As a biochemistry researcher and fitness enthusiast since my teens, I co-authored with my brother CJ, an international physique champion, the bestselling “This Body This Life,” which was featured in national radio, newspapers, and magazines. The book featured our own personal philosophies and our daily walk with health, fitness, and nutrition. Have a browse at my books.
I have always loved writing, and have been a published author since 1995, and a blogger since the late 1990s. I co-authored the book “Dot ZEN,” a leadership and entrepreneurship book aimed at small business owners, high-tech startups, knowledge entrepreneurs, and senior executives, to help them see a whole new way of managing marketing, publicity, public relations (PR), branding, human resources, entrepreneurship, and the use of the Internet, in a non-aggressive, enlightened manner. The book was based on 30 years of collective experience between us, when serving corporations and clients. As a biochemistry researcher and fitness enthusiast since my teens, I co-authored with my brother CJ, an international physique champion, the bestselling “This Body This Life,” which was featured in national radio, newspapers, and magazines. The book featured our own personal philosophies and our daily walk with health, fitness, and nutrition. Have a browse at my books.
Engage me to supercharge your business now!
Please fill in your details to engage me for public relations (PR) and strategic counsel, media training, crisis communications, and keynote speeches.
If you are a journalist who needs a friendly and credible source, you can look at my Qwoted profile, or contact me here.
 Tough Times, Great PR book out!
Tough Times, Great PR book out!




